Virtual care leaders struck a defensive tone at the annual ATA Nexus conference in Phoenix this week, denouncing the implication that recent business failures in the telehealth arena mean the care modality is on its way out. This is, in and of itself, not surprising. After all, one would expect a...
[RevCycleIntelligence]

Pandemic volume changes underscore rural hospital concerns
[HealthITSecurity]

Insider threats in healthcare remain prevalent
[PharmaNewsIntelligence]

Healthcare Realty Trust, KKR forge medical outpatient JV
[LifeSciencesIntelligence]
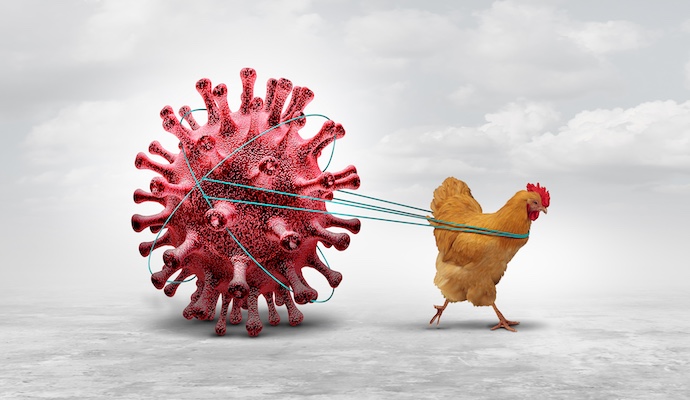
Caution urged as bird flu spreads among cattle and dairy workers
Do Not Sell or Share My Personal Information
©2012-2024 TechTarget, Inc. Xtelligent Healthcare Media is a division of TechTarget. All rights reserved. HealthITAnalytics.com is published by Xtelligent Healthcare Media a division of TechTarget.